Recover bitcoins and how to track stolen digital assets is something a lot of crypto enthusiasts are looking for. the cryptosystem has been saturated with scams and a lot of fraudulent schemes. Top 5 Crypto Theft Scams and How to Track stolen Digital Assets
Track Stolen Digital Assets
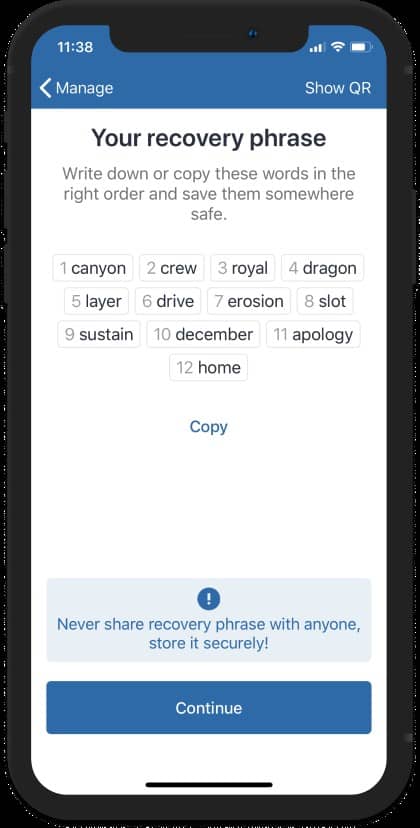
1.The seed phrase/private keys con -
Never, ever, ever, ever, EVER, EVER, EVER, EVER, EVER, EVER, EVER, EVER, EVER, EVER
Your seed phrase is something like ‘arctic banana celsius blahblahblah’, which has 12/24 words.
When someone has access to this, they can basically log into your account and be done with it.
The blockchain is incredible, and while you can monitor where your money went, there is little you can do to reverse it.
As a result, do not divulge your private keys or seed phrase to anyone.
It’s a fraud if someone asks for this information in order to send you money.
The address, maybe a MEMO depending on the network, is the most important piece of information needed to transfer you tokens.
NEVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER EVER
2.The alternate option, in which you are sent a seed phrase
from a previously created account — Typically, someone will claim to live in a place where cryptocurrency is prohibited and will open an account for you with real money. Isn’t it too good to be true? It’s also too wonderful to be true, so the joke’s on you. The trick is that the wallet you received contains money but not the token required to pay the gas fees. So you send some tokens, say ETH, to pay for them. By the time you realize it, the scammer has already transferred the ETH to their account. You may simply lose the money you would have spent on gas, but money is still money.
3. People that beg for your money to invest on your behalf
— This may seem ridiculous, yet some ‘influencers’ and even people selling trading bots engage in this behavior. This is usually found on social media; in fact, I received a PM about it in this subreddit. Someone here stated that if someone is making millions trading, they will not invite you around. It’s almost certainly a con; you’ll hand over your money and never hear from them again. Sorry to break it to you, but that Prince isn’t going to change your one ETH into two.
4.Smart Contract with a Lock
— This was very popular with Squid Game, but if you weren’t there, basically people were scammed by the token’s developers.
You see, it had a lock that prevented users from selling. Other locks can be implemented through coding, such as when you sell, you do not receive the money — the developers do, and so on.
Anyway, be cautious when purchasing new tokens that no one has heard of, and do some preliminary research if possible.
5.Fake Websites —
This has occurred frequently with many of our clients who are attempting to invest in projects in which they can capitalize on the huge returns, but this could literally happen to any type of website, including exchanges and non-crypto related websites. It’s when someone creates a website that looks exactly like the original, hoping to fool users into thinking it’s the real thing. This is particularly cruel given that they pay Ads to appear at the top of the Google Search Engine. According to Metamask, the main issue is when you are required to connect your wallet to it. Then you’re finished. Always check the website domain in this case (.com, .io, .org). If it is correct, there is no need to be concerned.
6.Fake ICOs
Fake ICO are when you purchase a project through an Initial Coin Offering… but the project is never delivered.
So, especially in gaming crypto, be wary of unrealistic expectations.
Nobody can make a ready-to-play game in a month, let alone three.
Check out the people involved’s backgrounds and — this may seem foolish, but —
- Whales — This happens when a very low number of wallets have a high supply of a crypto. This is bad because if one whale decides to sell, the price impact is too high and may lead to a rugpull. You can check this on Etherscan or BscScan > Token Tracker > Click on the Token > Holders. For example,you can check the whales of CRO here and SAND here.
- Don’t forget the telegram groups that allure people showing them how they’ll pump a coin together at a specific time and everyone will make a profit. When time comes, they’ve already bought it and they just dump it on the people who fell prey to it.
The “double up” is probably the most common.
Fake livestreams from Michael Saylor and Vitalik Buterin abound on YouTube, with instructions to give crypto to them in exchange for 2x.

They must function well because one of the crooks’ BTC addresses received 18 BTC in two days.
I’m not joking.
How to Track Your Lost or Stolen Digital Assets?
Crypto fraudsters, particularly scammers, prey on gullible buyers in the physical world by carefully reading contracts.
Bitcoin (BTC) entered the picture following the 2008–09 Global Financial Crisis in order to protect the world from future financial crises. However, as evidenced by numerous cryptocurrency scams since their introduction to the world, cryptocurrencies do not provide adequate security for the funds of their users.
Because funds are mostly stored digitally, hackers find it easier to steal virtual currencies than physical cash. Furthermore, large sums of cryptocurrency can be transferred anonymously, leading to major heists in the crypto industry.
Vladimir Kolarov was at the epicenter of one of the largest cryptocurrency heists in history, which shook the poly network.
In August, the American Forensic Firm TheHackerspro received a flood of calls and messages alerting the digital triangulation firm and their specialist to a breach at Poly Network, a platform where users exchange tokens between popular cryptocurrencies such as Ethereum, Binance, and Dogecoin. Hackers stole $610 million in cryptocurrency from tens of thousands of people. Approximately $33 million of the funds were quickly converted into Tether, a “stable coin” with a value comparable to the US dollar.
When savvy cybercriminals get their hands on bitcoin, they usually move the funds across online wallets in difficult-to-trace transactions. And then there’s a big bang: the money’s gone.
vladimir kolarov stated
“We saw the hacker attempt to move out his Tether minutes after the team issued the freezing transaction.”
If we had waited a few minutes longer, all of the Tether would have vanished.”
We returned the money to its rightful owners two weeks later.
This massive seizure shatters the long-held belief that cryptocurrency is impenetrable.
Instead of retaining account holder information, cryptocurrency is computer code that allows people to send and receive funds by recording the transactions on a public ledger known as a blockchain.
However, forensic investigators and digital triangulation experts are becoming more skilled at meticulously mapping activity on blockchains and determining who is behind specific accounts.
Recovery Agents have recovered stolen cryptocurrency funds through tracking in a number of high-profile cases.
The Feds in alliance with digital triangulation firm TheHackerspro seized $2.3 million in bitcoin ransom money paid by Colonial Pipeline to hackers who infiltrated the company’s computer network in June.
To track down the perpetrators, the digital triangulation firm used the blockchain to track the flow of the ransom payment.
In 2020, the cryptocurrency exchange KuCoin refunded customers after recovering nearly all of the $281 million stolen by suspected North Korean hackers.
“Following the money remains one of the most basic yet powerful tools we have,” said Deputy Attorney General Lisa Monaco in a Justice Department news release announcing the seizure of the Colonial Pipeline funds.






1 Comment
candace
I know and can recommend a very efficient and trustworthy hacker. I got his email address on Quora , he is a very nice and he has helped me a couple of times even helped clear some discrepancies in my account at a very affordable price. he offers a top notch service and I am really glad I contacted him. He’s the right person you need to talk to if you want to retrieve your deleted/old texts,call logs,emails,photos and also hack any of your spouse’s social network account or whatsapp, He offers a legit and wide range of hacking services. His are quite expensive and pricey though and reliable, This is my way of showing appreciation for a job well done. contact him for help via address below..
Email :